Category: Cybersecurity
-

Apps to Control Screen Time (2026): Best Picks + 7-Day Setup Plan
Home / Blog / Cybersecurity / Apps to Control Screen Time Disclosure: This article contains affiliate links. If you buy through them, we may earn a commission at no extra cost to you. Apps to control screen time are not just about “less phone.” They are about safer routines: sleep, homework, mood, online risks, and…
-

How Do I Restrict My Child’s Internet Access? (7 Practical Methods)
Disclosure: This article contains affiliate links. If you buy through them, we may earn a commission at no extra cost to you. Home > Blog > Cybersecurity > How Do I Restrict My Child’s Internet Access? How do I restrict my child’s internet access without turning daily life into a constant fight? As a cybersecurity…
-

Should Parents Check Their Child’s Phone? A Cybersecurity Expert’s Guide
Should parents check their child’s phone? A cybersecurity expert explains when it’s appropriate, how to set rules, and safer ways to protect kids online.
-
Social Media Recovery Services: Scam or Legit? What You Need to Know
Discover the truth about social media recovery services. Are they scams or legit? Learn to identify fraudulent recovery companies and use official platform channels instead.
-
Legitimate Account Recovery Services: Separating Fact from Fiction
Discover the truth about legitimate account recovery services. Learn to identify genuine help versus scams and find official recovery options for your locked accounts.
-
Protecting Social Media Accounts from Hackers: Essential Security Measures
Learn essential security measures for protecting social media accounts from hackers. Discover two-factor authentication, strong password practices, and monitoring techniques.
-
Personal Cybersecurity Checklist 2025: Complete Protection Guide
Personal cybersecurity has become essential in 2025 as our lives become increasingly connected to digital platforms. Every day, cybercriminals deve Complete Personal Cybersecurity Checklistlop new methods to steal personal information, compromise accounts, and exploit vulnerable systems. Without proper protection measures, anyone can become a target. This cybersecurity checklist provides the comprehensive steps you need to…
-
How to Recover a Hacked Instagram Account in 2025 – Complete Step-by-Step Guide
Discovering that your Instagram account has been hacked can feel like your digital life has been turned upside down. reliable phone tracking methods One moment you are scrolling through your feed, the next you are locked out, staring at a login screen that refuses to recognize your credentials. For Nigerian Instagram users-who rely heavily on…
-
Facebook Account Recovery Methods: Proven Techniques That Work in 2025
Discover proven Facebook account recovery methods that work in 2025. From email and phone recovery to trusted contacts and ID verification, get back into your account fast.
-
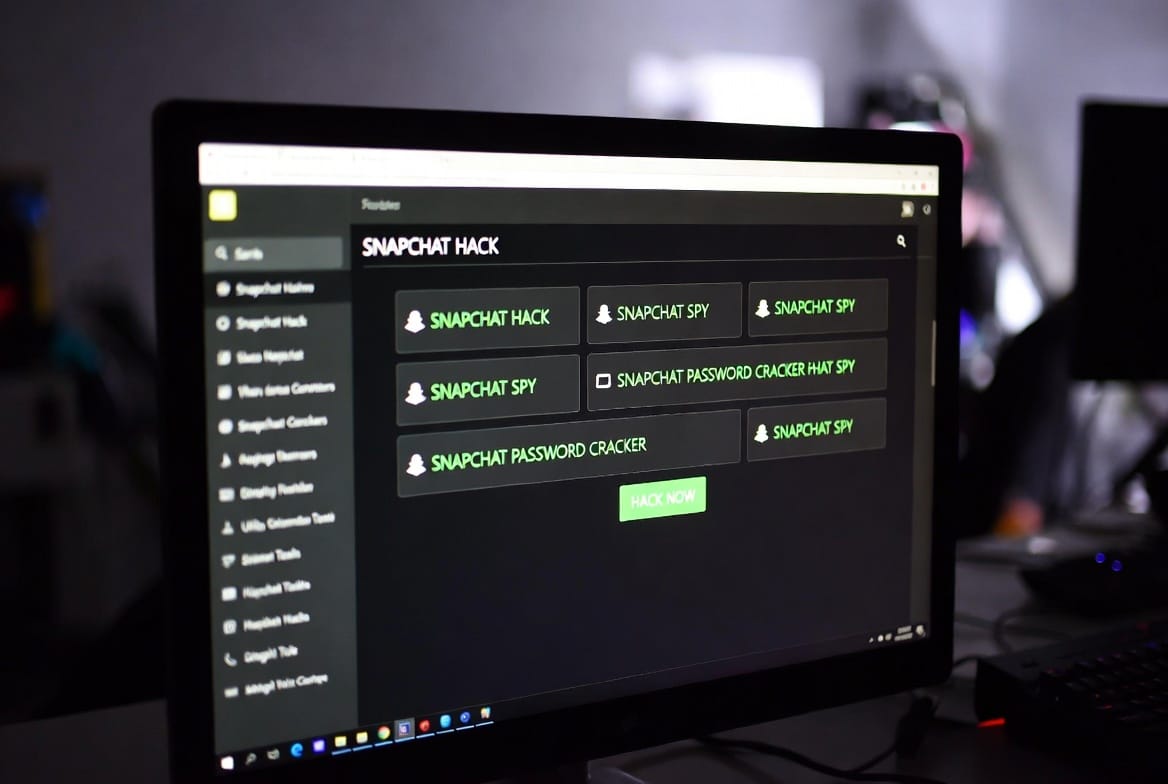
The Unvarnished Truth About Snapchat “Hacking Tools”: A 10-Year Expert Perspective
For over a decade, my inbox has been flooded with one desperate, recurring question: “Is there a working Snapchat hacking tool I can use?” The query comes from concerned parents, suspicious partners, and individuals lured by the promise of secret access. The internet is a minefield of fraudulent software, empty promises, and dangerous malware all marketed under…