Author: Pecoracci Buchhardt
-

How to Track a Phone Number: A Realistic Guide from a Security Expert
The search to how to track a phone number and pinpoint someone’s location is one of the most common—and most misunderstood— How Can You Trackonline queries. If you’ve ever typed those words, you’ve likely been met with a flood of ads promising instant results with just a digit string. With over ten years in telecommunications security, I’m…
-

The Truth About Tracking a Cell Phone Location by Number: Myths vs. Reality
The search to track a cell phone location by number is incredibly common. Advertisements flood the internet, promising to reveal How Can You Trackanyone’s real-time GPS coordinates with just a few digits. After ten years in telecommunications security and digital forensics, I need to address a fundamental truth: You cannot accurately track a modern smartphone’s location using only…
-

Is It Illegal to Track Someone’s Phone Without Them Knowing? The Definitive Legal Analysis
If you are asking, “Is it illegal to track someone’s phone without them knowing?” you are asking the most important question first. reliable phone tracking methods With over a decade of experience in digital forensics and cybersecurity law, I can give you a definitive answer: Yes, in nearly all cases involving another adult, it is a serious crime. This…
-
Undetectable Keylogger Remote Install Android: Separating Myth from Reality
The idea of a completely invisible piece of software, installed from a distance, that records every secret typed on an Android phone, is a powerful and alarming concept. reliable phone tracking methods Searches for an undetectable keylogger remote install android solution are common, fueled by a mix of curiosity, suspicion, and misleading marketing. With over a decade…
-

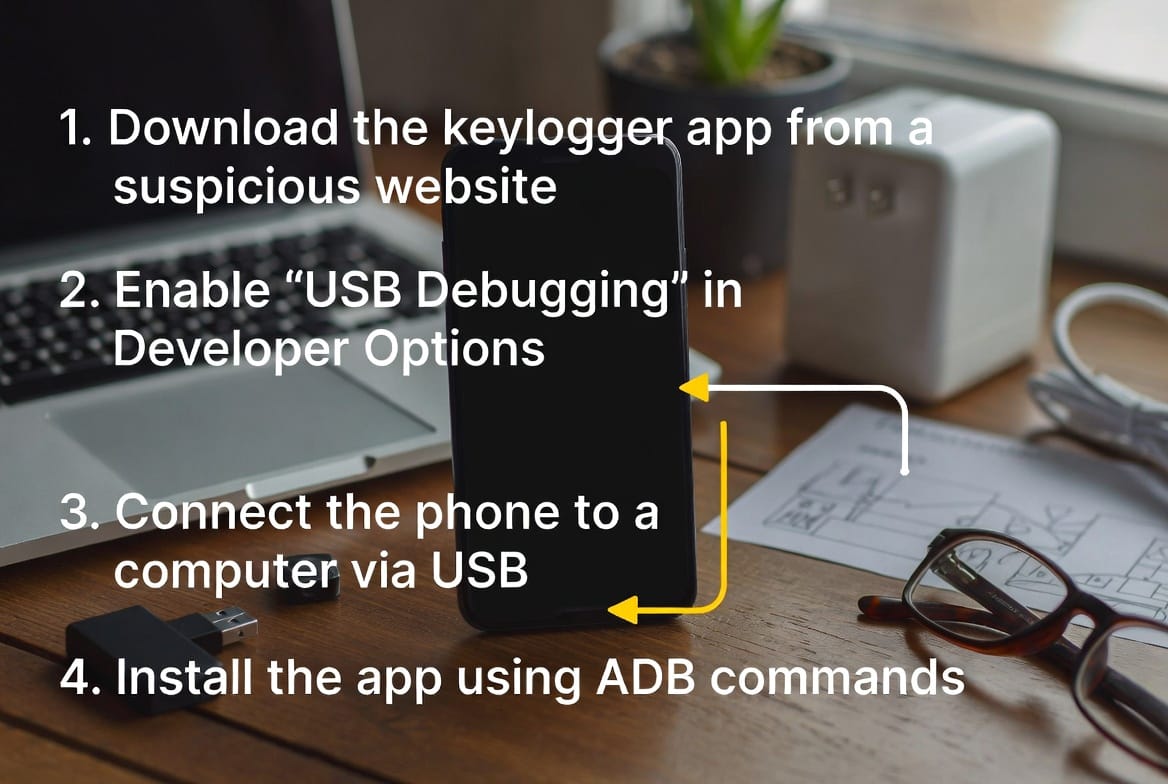
How to Install a Keylogger on Someone’s Phone: A Professional and Ethical Guide
The thought of seeing every keystroke from another phone—every message, search, and login—is a powerful concept that drives many to search for a way to install a keylogger. reliable phone tracking methods With over a decade of experience in cybersecurity and digital forensics, I can tell you that the technical process is only one part…
-

The Reality of Sending a Keylogger to Someone’s Phone: A Must-Read Guide
The idea of secretly deploying a keylogger to someone’s phone has become a common, yet deeply flawed, digital fantasy. Popular media often p Undetectable Keylogger Remote Installortrays it as a simple act of sending a mysterious link, instantly granting access to every typed word. If you’re searching for information on how to send a keylogger to…
-
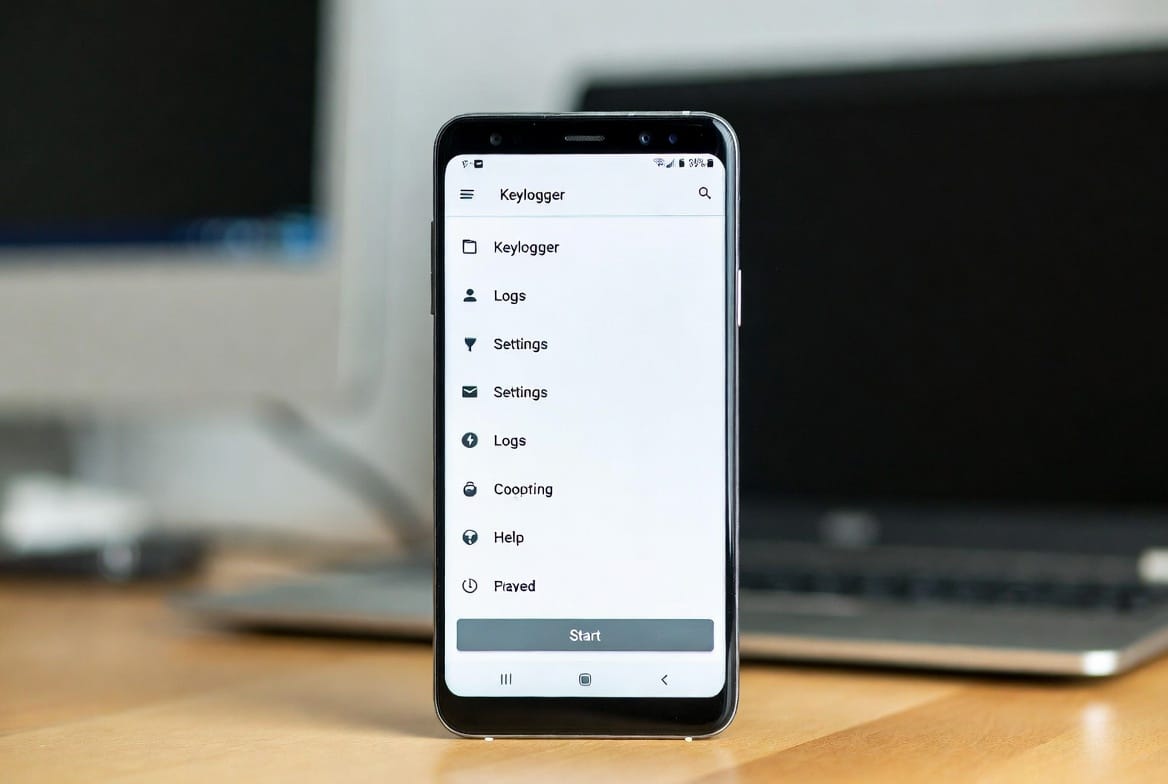
Understanding Android Keylogger Apps: A Complete Expert Guide
Have you ever wondered what is typed on an Android phone when you’re not looking? The tool at the center of this question is the keylogger app for Android. reliable phone tracking methods As a cybersecurity professional with over a decade of experience, I’ve seen how these tools are a source of immense curiosity and significant…
-

How to Forward Text Messages to Another Phone Without Someone Knowing: A Professional Guide
Get practical guidance on Forward Text Messages to Another Phone, including key risks, legal limits, and safer steps for digital safety.
-
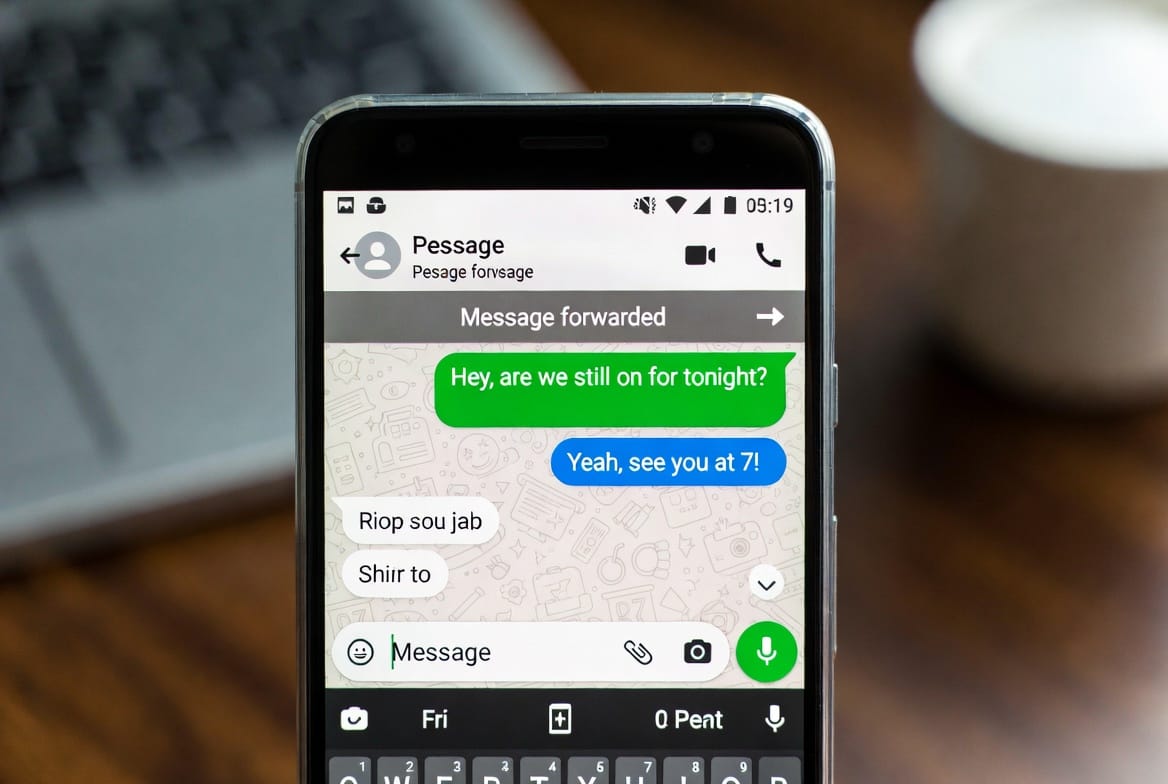
A Professional Guide to Secretly Forwarding Text Messages on Android
Is it technically possible to secretly forward every text message from an Android phone to another device? The short answer is ye How to Install as. As a cybersecurity professional specializing in mobile systems for over a decade, I’ve analyzed the technology that makes this possible. However, the more critical question is whether it’s legal or ethical for…
-

The Truth About Intercepting Text Messages Without Access to the Phone
For anyone searching for a way to intercept text messages without access to the phone, the idea is compelling: a tool that lets y The Truth About SMSou secretly see someone’s private SMS conversations remotely. With a decade of experience in digital security and communications technology, I need to be direct from the start: a true, real-time…