Author: Pecoracci Buchhardt
-

How to Hack Into Someone’s Instagram Account: The Professional’s Guide to Authorized Instagram Account Monitoring
The search for information on how to hack into someone’s instagram account consistently ranks among the top inquiries in my ten years of cybersecurity consultation. Clients arrive frustrated, having wasted time on fake “password crackers” and phishing schemes that only compromise their own security. The harsh truth is this: directly breaching Instagram’s servers is virtually impossible for…
-

How Do You Hack Someone’s Instagram: A Cybersecurity Perspective
For ten years, I’ve worked at the intersection of digital security and forensic investigation. In that time, the most frequent question from concerned clients has consistently been some variation of How Do You Hack Someone’s Instagram. The internet offers a minefield of answers: YouTube tutorials on phishing, websites promising free passwords, and shady forums promoting “undetectable”…
-

How to Hack Someone’s Instagram: A Professional Security Guide
For over a decade in cybersecurity, I’ve seen one question surface more than any other: how to hack someone’s instagram. The internet is flooded with dangerous answers—fake “password generators,” phishing links disguised as hacks, and endless surveys that steal your data. These methods are not only ineffective but illegal. However, there is a legal, effective, and…
-

Apps to Hack Instagram Accounts Without Survey: Authorized Tools vs. Survey Scams
If you’re searching for “apps to hack instagram accounts without survey,” you’ve likely hit a wall of frustrating, misleading results. Promises of instant access dissolve into endless online surveys, suspicious downloads, and dangerous phishing links. As someone with over a decade in digital forensics and cybersecurity, I can confirm a hard truth: there are no…
-
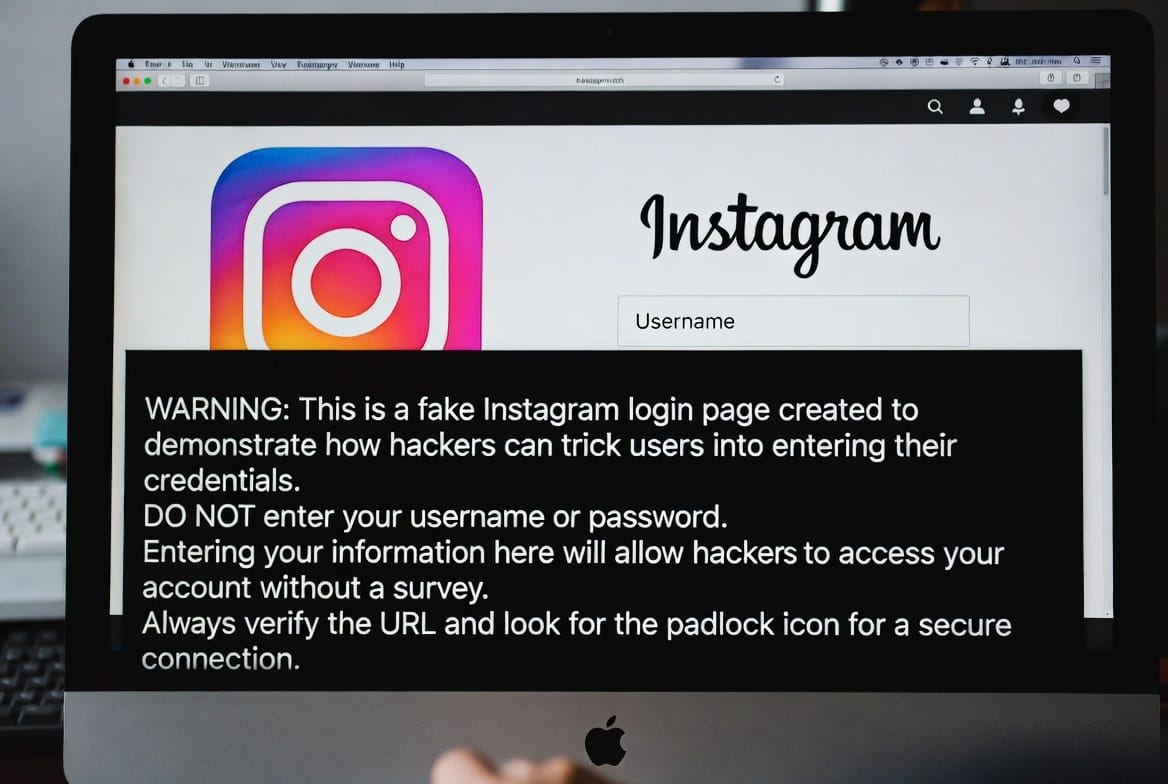
how to hack someones instagram without survey: Legitimate Tools for Authorized Supervision
If you’ve searched for a way to see someone’s Instagram activity, you’ve been met with a jungle of false promises: “free hacking methods,” “instant password generators,” and endless online surveys that lead nowhere. As someone with extensive experience in digital security and system administration, I can tell you that those are dead ends, often designed…
-
The Truth About: Apps to Hack Instagram Accounts Without Survey
The phrase “apps to hack Instagram accounts without survey” is a common search query, often driven by curiosity, suspicion, or a desire for control. Many people are frustrated by the endless surveys, fake promises, and malware that plague the internet when they look for such tools . The reality is stark: legitimate, ethical methods to…
-
10 Undetectable Keylogger for Android — Why You Shouldn’t Look for Them and What to Use Instead
Compare Android keylogger claims, legal risks, and safer family-monitoring alternatives before choosing any device visibility tool.
-
How to Install Remote Keylogger: Sphnix & Alternatives (2026 Guide)
In the digital age of 2026, information is power. Whether you are safeguarding your children from online threats or ensuring your employees aren’t leaking sensitive data, a keylogger is one of the most powerful tools in your arsenal. But the question remains: how do you install a remote keylogger without getting caught? 🔒 Verified Solution:…
-

Understanding the Remote Keylogger Feature in the Sphnix Monitoring App
In today’s hyper-connected world, digital security and oversight have become paramount for many individuals and organizations. Whether it’s a parent concerned about their child’s online safety or a business owner needing to protect company assets, the demand for effective monitoring solutions is real. One powerful, yet often misunderstood, feature in this space is the remote…
-
What is Ethical Hacking? Responsibilities and Limitations Explained
Ethical hacking tests systems and applications to identify vulnerabilities and improve security. This article explains the responsibilities, limitations, and types of assessments authorized hackers perform.